A lot of HP PC and laptop owners complained about a Caps Lock notification popping up on their screens. Here's how to tu
22 hours ago



A lot of HP PC and laptop owners complained about a Caps Lock notification popping up on their screens. Here's how to tu
22 hours ago
Lenovo launched the latest line of laptops and it's slashing the prices on older models. Grab your ThinkPad P16v Gen 1 w
22 hours ago
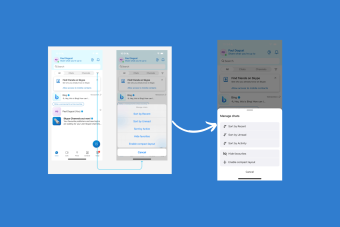
Microsoft Copilot will be capable of generating SWOT analysis, potentially sparring SMBs of big money in the long run. H
22 hours ago
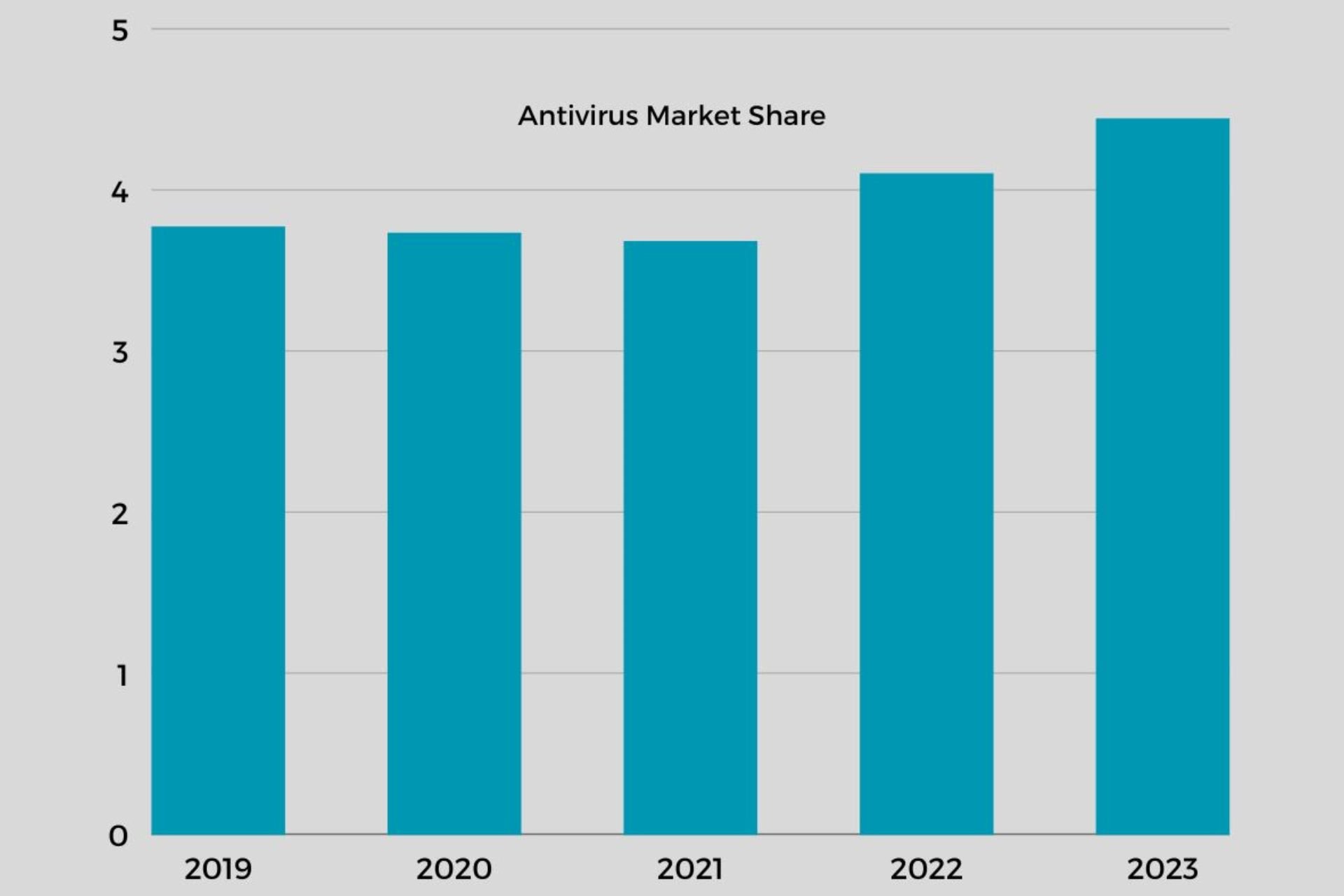




We highlights the best surveys, research or exclusive materials our team has manually researched and published. In this section you’ll find key information about the Windows world.
Upgrade your browsing experience now!

Get built-in VPN, ad-blocker, high speed, and exclusive game mode. Try Opera Today!